Zero Trust: Secure for Tomorrow’s Threats, Not Yesterday’s
In a world where attackers move faster than ever, the old “trust but verify” model no longer works.
Zero Trust flips the equation: never trust, always verify.
It’s not new. The term was coined in 2010, gained traction in the mid-2010s, and became even more visible after the U.S. federal mandate in 2021.
Today, Zero Trust is more than a framework — it’s a survival strategy.
For VCs, private equity firms, and financial services, the stakes are even higher because these organizations are prime targets for attackers, as seen in recent breaches where financial data and deal pipelines have been exposed.
Zero Trust is not just relevant here — it’s essential to protecting sensitive information, investor trust, and deal flow.
What is Zero Trust Really?
Zero Trust isn’t a single product or checklist — it’s a mindset.
And depending on your perspective, you can look at it in different ways.
One way is through the lens of how trust is established and verified. Every access request should be evaluated against multiple attributes.
For example: Imagine an employee trying to open a confidential financial file. Before access is granted, the system checks:
• Identity – Is this really the employee logging in, and are they authenticated with MFA
• Device – Is the laptop patched, encrypted, and free from malware?
• Location – Are they connecting from the office network, or suddenly from another country?
• Behavior – Does this match their normal work pattern, or is it unusual activity at 2 a.m.
• Access – Do they actually have permission to view this file?
Only if all these conditions are satisfied is access allowed. This continuous, contextual verification is the essence of Zero Trust.
Another perspective is where Zero Trust should be applied — across the core domains of your environment:
• Endpoint Security
• Application Security
• Data Security
• Cloud Security
• Network Security
• IoT Security
• API Security
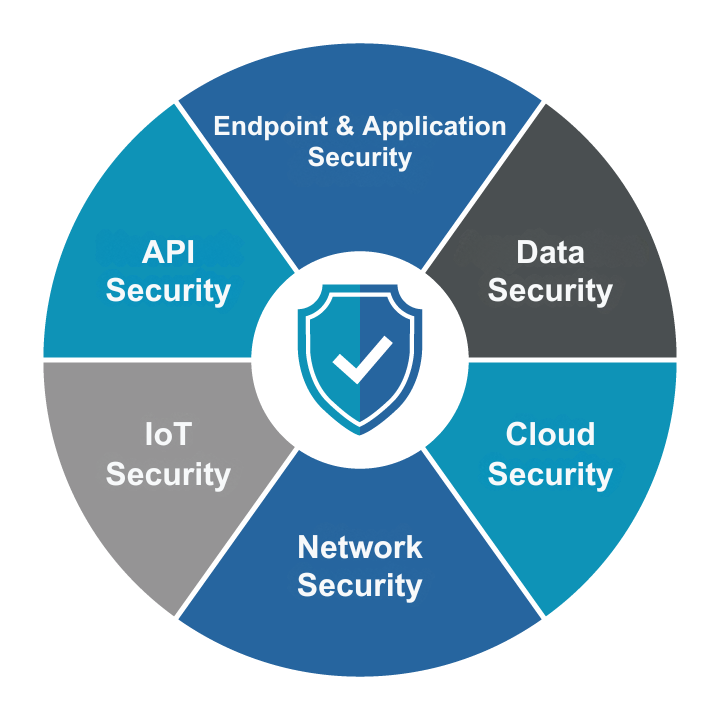
This domain-based view helps organizations assess where Zero Trust controls are strong, and where critical gaps still exist.
Overlooked Domains & Forgotten Devices
Some Zero Trust domains get more attention than others.
Endpoints, Applications, Data, and Cloud often take center stage because they’re easier to secure and supported by mature, ready-to-deploy products. In many cases, you can improve security and convenience at the same time simply by adopting a well-known solution.
But not all domains are this straightforward. IoT, APIs, and Network Infrastructure frequently receive less attention because they are complex, less familiar, or require specialized expertise. In some cases, newer solutions have even oversimplified security in the name of convenience.
The same problem applies to forgotten devices. Printers, cameras, badge readers, IoT sensors, or even AV systems like Sonos and Apple TVs often sit outside the Zero Trust model. They’re dismissed with arguments like:
• “They don’t store or carry data.”
• “They’re behind a firewall — they’re safe.”
• “We’re not a big target, who would hack us?”
Yet these devices can and do play a role in attacks: printers often cache sensitive documents, cameras can be hijacked to capture credentials, and APIs are one of the top causes of modern breaches.
If your Zero Trust model stops at laptops and servers (or even cloud and identity), you’re not truly Zero Trust. Make sure all domains get the required attention. Do not simply ignore some.
Secure for Tomorrow’s Threats, Not Yesterday’s
Zero Trust cannot stop at a handful of areas — it must eventually extend across every domain and device. Partial adoption leaves gaps, and attackers thrive on the smallest cracks in coverage.
Modern threats don’t just target obvious systems. Attackers now use cameras, microphones, and even keystroke patterns to gather data for deepfakes, AI-driven reconnaissance, and sophisticated social engineering campaigns. Ignoring IoT devices or APIs gives them the exact fuel they need.
And while some argue that network and IoT security is dead, the opposite is true.
With a growing number of IoT devices — security cameras, Sonos systems, audio/video devices, and more — network and IoT security is as relevant as ever. The difference is that it must evolve: microsegmentation, software-defined perimeters, continuous monitoring, and least privilege access are now the essential pillars.
To stay secure, organizations should start by mapping their environment against these domains, identifying gaps, and prioritizing high-risk areas like APIs and IoT devices. Zero Trust must cover every domain, every device, and every access point. Anything less leaves yesterday’s defenses against tomorrow’s threats.
Want to know if your Zero Trust strategy is complete?
